Single Sign On – A simple and convenient way of combining TimeTac with your existing systems
by Magdalena Fladl, 03.03.2020
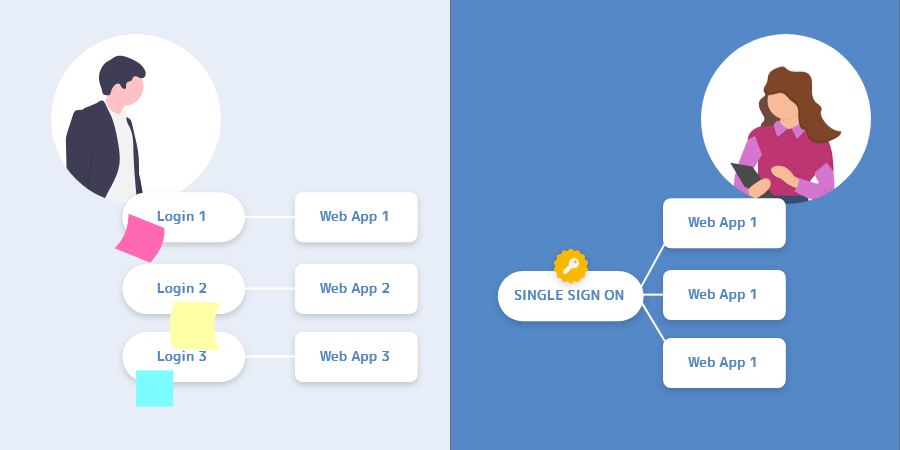
Organizing services and different tools used in daily work can become a very extensive activity. Companies that aim to focus on their core product and task tend to outsource support activities (such as project management and time tracking) to third party software solutions. At some point, employees have lots of different services, various accounts followed by a large number of usernames and passwords. This can affect the effectiveness of the processes and make repetitive tasks more complex.
What is Single Sign On?
SSO offers the possibility to access multiple applications with a single set of credentials, which means that you have a single username/password combination that opens all the software your company uses in daily activities! In order to make this possible, SSO combines two important entities: “Identity Provider” and “Service Provider”.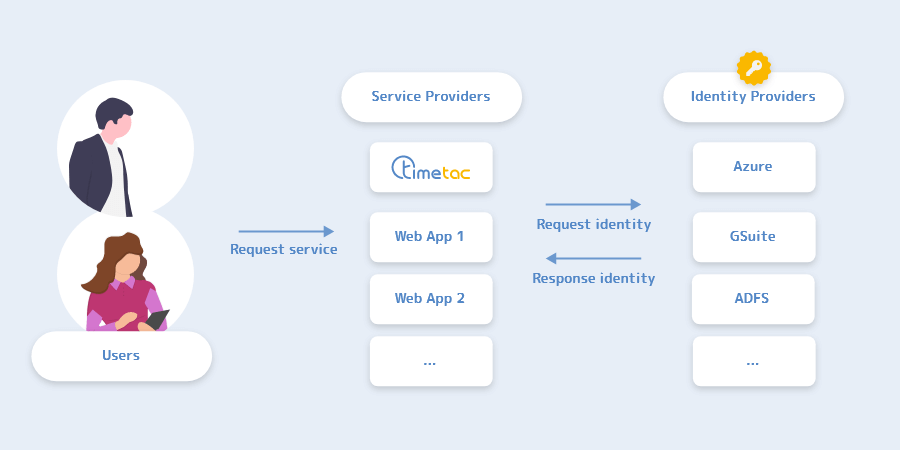
What are the benefits of Single Sign On for your company?
What are the concerns regarding SSO?
The process of SSO implementation requires technical expertise as SSO has to be configured at both sides (identity provider and service provider). This is an important concern for companies who are implementing SSO because this might be a new activity for them.We have large companies as customers with thousands of employees and they are already using SSO with different services. In these cases, implementation is usually simple because they make one additional configuration for TimeTac.
However, sometimes we work together with companies who are implementing SSO for the first time and find this technically challenging. This is why our integrations team created detailed technical tutorials to help our customers set up SSO for providers such as Azure, Active Directory ADFS and GSuite.
We are always happy to share our knowledge with our customers and support them to integrate TimeTac into their systems. What makes me happy is that we are able to successfully integrate and support companies with different sizes and backgrounds, making TimeTac a valuable part of their services family.
What are the requirements for Single Sign On?
The most important requirement for SSO is to have an identity provider. Companies that want to introduce SSO must have a working identity provider. Common examples of identity providers are Microsoft Azure, Google GSuite or Active Directory with ADFS. TimeTac is a service provider. SSO cannot work without an identity provider on the other side. If there is no identity provider in use yet, find an identitiy provider that suits your company’s needs, configure it and then conctact TimeTac to continue with SSO. If an identity provider is already being paid for (and used), SSO is a benefit that should definitely be used.Should customers already have a SSO expertise?
Companies and TimeTac customers who want an SSO don’t have to be experienced in setting up SSO.As I already said, we are always happy to share our knowledge with our customers and support them with the integration of TimeTac into their systems. Actually, we created high-quality tutorials for our customers, describing how to configure the identity provider for SSO. We did this for Azure, ADFS and for GSuite as well. In the future, we are planning on doing it for even more identity providers.
Each of our customers has constant technical support from my team during the SSO implementation. We have only positive experiences from working with our customers. There are challenges from time to time but we solve them and every time it results in having an even better knowledge base that we can share.
The important detail is that SSO is a configuration that has to be done from both sides. We have to configure something, our customers have to configure something. We cannot configure it for them, but we can provide them with support.
What are the common challenges for our customers when they are setting up SSO from their side?
A challenge that companies encounter when they do not have an identity provider is to find a proper one. Large companies have detailed processes and procedures when something new has to be implemented. Therefore, finding and implementing an identity provider can take time, meaning when companies are planning to implement SSO they should plan to find an identity provider first and not start with SSO before that. Companies with an already available identity provider usually do not have to face big challenges. However, there is a difference between cloud identity providers (Azure, GSuite) and self-hosted local identity providers (ADFS).Cloud providers come with predefined configurations that cannot be changed that much. That makes setup and maintenance easier. Self-hosted local identity providers are installed and configured by companies. This can result in having lots of different and unique configurations which can make SSO setup a bit more challenging. As a general rule of thumb, setting up SSO with Azure, for example, will be faster and more straightforward than an SSO setup with ADFS.
How does the actual SSO implementation process look like?
Firstly and most importantly, if you want to implement SSO you should have an identity provider. Then you should send a request (ideally in the form of a ticket or direct email to our customer care) asking for an SSO quote. If the identity provider is in a list of supported ones, a standard quote will be provided. If there is any custom work involved, the custom quote will be provided.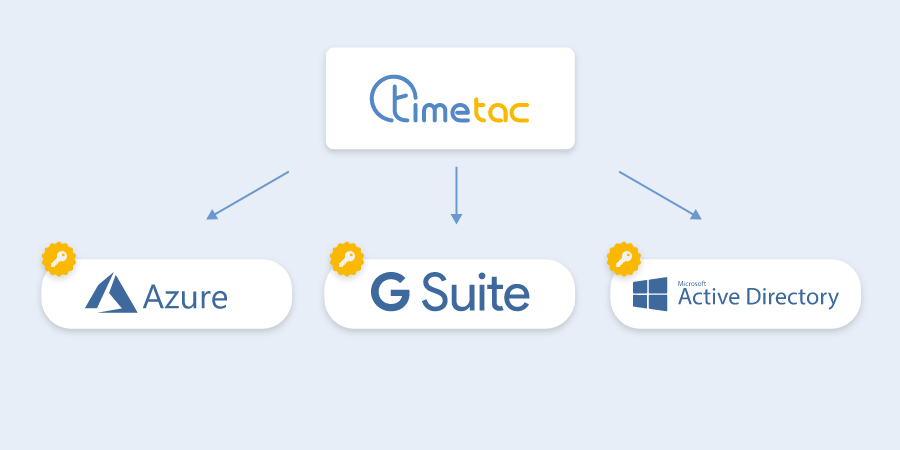
How much time does it usually take for a customer to get a configured and working SSO?
Typically, a configuration of the SSO is done within a working week from the moment when a customer orders it and accepts the quote.But what happens if the customer already did an SSO configuration for the other software?
SSO has to be configured for each software (service provider). It is beneficial when a customer has already configured it because they will have more experience, but still, they have to configure it again for TimeTac.What SSO method can you select for TimeTac?
Currently, we support several identity providers by default:This blog post was supported by Milan Latinović, Lead Integration Engineer at TimeTac.
Ready to Simplify Your Time Tracking
With TimeTac you manage your working hours easily and efficiently.